This guide will show you to install Microsoft (Classic) Teams and deploy Microsoft Teams VDI Optimization on VMWare Horizon for Manual Pools, Automated Pools, and Instant Clone Pools, for use with both persistent and non-persistent VDI. This guide works for Microsoft Teams on Windows 10 and Windows 11, including the new Windows 11 22H2.
Please see my post Deploy and install the New Teams for VDI to learn how to deploy the new Teams client for VDI. The Classic client will go end of support on June 30, 2024.
Please make sure to check out Microsoft’s documentation on “Teams for Virtualized Desktop Infrastructure“, and VMware’s document “Microsoft Teams Optimization with VMware Horizon” for more information.
I also have a guide on how to Deploy, Install, and Configure Microsoft Office 365 in a VDI Environment, so make sure you check it out!
Requirements
To get started, you’ll need the following:
- Microsoft Teams MSI Installer (Available here: 64-Bit, 32-Bit)
- VMware Horizon Client (Available here)
- VDI Desktop or VDI Base Image
- Ability to create and/or modify GPOs on domain
- VMware Horizon GPO Bundle
Background
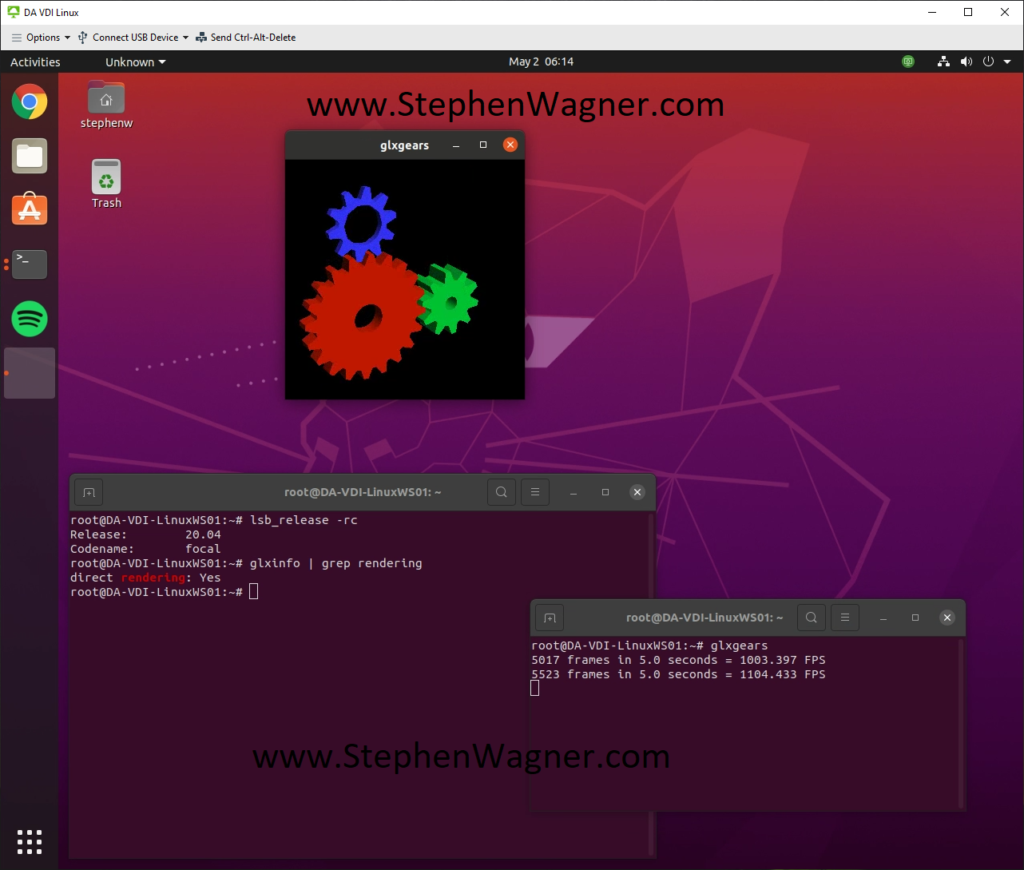
Before Microsoft Teams VDI Optimization, VMware’s RTAV (Real-Time Audio-Video) was generally used. This offloaded audio and video to the VMware Horizon Client utilizing a dedicated channel over the connection to optimize the data exchange. With minor tweaks (check out my post on enhancing RTAV webcam with VMware Horizon), this actually worked quite well with the exception of microphone quality on the end-users side, and high bandwidth requirements.
Starting with Horizon View 7.13 and Horizon View 8 (2006), VMware Horizon now supports Microsoft Teams Optimization. This technology offloads the Teams call directly to the endpoint (or client device), essentially drawing over the VDI VM’s Teams visual interface and not involving the VDI Virtual Machine at all. The client application (or thin client) handles this and connects directly to the internet for the Teams Call. One less hop for data, one less processing point, and one less load off your server infrastructure.
Microsoft Teams Optimization uses WebRTC to function.
Deploying Microsoft Teams Optimization on VMware Horizon VDI
There are two components required to deploy Microsoft Teams Optimization for VDI.
- Microsoft Specific Setup and Configuration of Microsoft Teams
- VMware Specific Setup and Configuration for Microsoft Teams
We’ll cover both in this blog post.
Microsoft Specific Setup and Configuration of Microsoft Teams Optimization
First and foremost, do NOT bundle the Microsoft Teams install with your Microsoft 365 (Office 365) deployment, they should be installed separately.
We’re going to be installing Microsoft Teams using the “per-machine” method, where it’s installed in the Program Files of the OS, instead of the usual “per-user” install where it’s installed in the user “AppData” folder.
Non-persistent (Instant Clones) VDI requires Microsoft Teams to be installed “Per-Machine”, whereas persistent VDI can use both “Per-Machine” and “Per-User” for Teams. I use the “Per-Machine” for almost all VDI deployments. This allows you to manage versions utilizing MSIs and GPOs.
Please Note that when using “Per-Machine”, automatic updates are disabled. In order to upgrade Teams, you’ll need to re-install the newer version. Take this in to account when planning your deployment. If you use the per-user, it will auto-update.
For Teams Optimization to work, your endpoints and/or clients MUST have internet access.
Let’s Install Microsoft Teams (VDI Optimized)
For Per-Machine (Non-Persistent Desktops) Install, use the following command:
msiexec /i C:\Location\Teams_windows_x64.msi ALLUSER=1 ALLUSERS=1For Per-User (Persistent VDI) Install, you can use the following command:
msiexec /i C:\Location\Teams_windows_x64.msi ALLUSERS=1If in the event you need to uninstall Microsoft Teams to deploy an upgrade, you can use the following command:
msiexec /passive /x C:\Location\Teams_windows_x64.msiAnd that’s it for the Microsoft Specific side of things!
VMware Specific Setup and Configuration for Microsoft Teams Optimization
When it comes to the VMware Specific Setup and Configuration for Microsoft Teams Optimization, it’s a little bit more complex.
VMware Horizon Client Installation
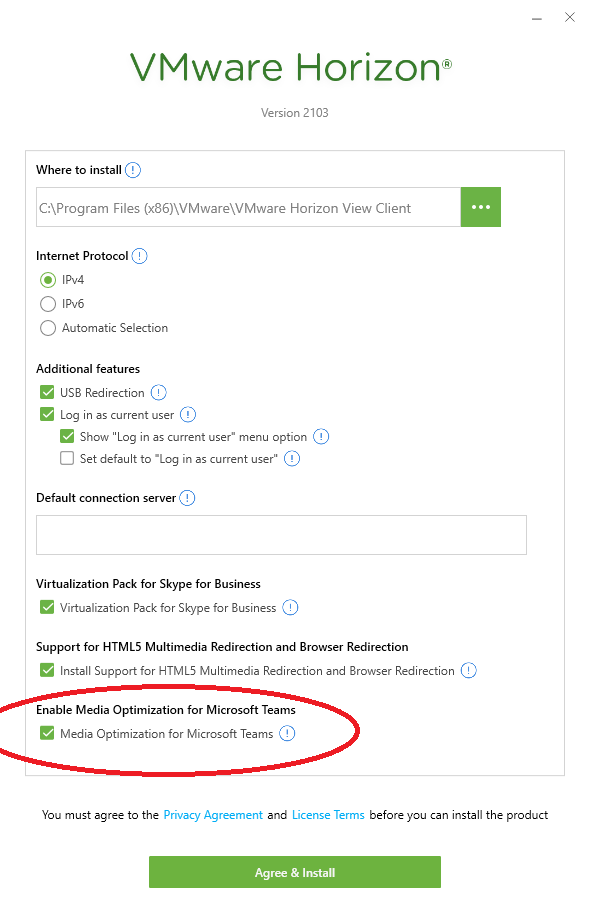
When installing the VMware Horizon Client, the Microsoft Teams optimization feature should be installed by default. However, doing a custom install, make sure that “Media Optimization for Microsoft Teams” is enabled (as per the screenshot below):
Group Policy Object to enable WebRTC and Microsoft Teams Optimization
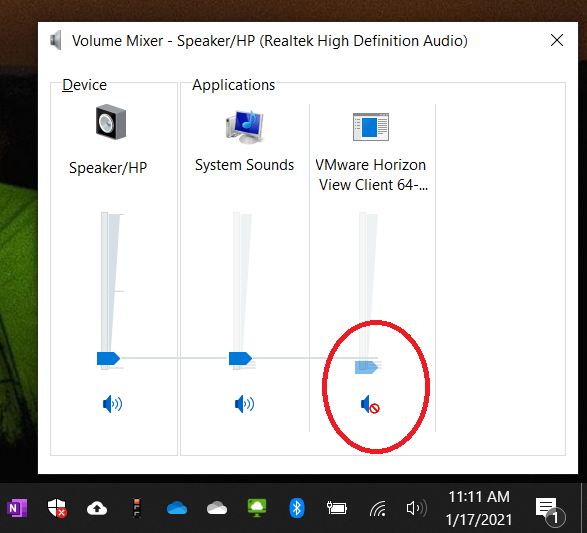
You’ll only want to configure GPOs for those users and sessions where you plan on actually utilizing Microsoft Teams Optimization. Do not apply these GPOs to endpoints where you wish to use RTAV and don’t want to use Teams optimization, as it will enforce some limitations that come with the technology (explained in Microsoft’s documentation).
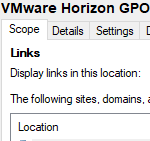
We’ll need to enable VMware HTML5 Features and Microsoft Teams Optimization (WebRTC) inside of Group Policy. Head over and open your existing VDI GPO or create a new GPO. You’ll need to make sure you’ve installed the latest VMware Horizon GPO Bundle. There are two switches we need to set to “Enabled”.
Expand the following, and set “Enable HTML5 Features” to “Enabled”:
Computer Configuration -> Policies -> Administrative Templates -> VMware View Agent Configuration -> VMware HTML5 Features -> Enable VMware HTML5 FeaturesNext, we’ll set “Enable Media Optimization for Microsoft Teams” to “Enabled”. You’ll find it in the following:
Computer Configuration -> Policies -> Administrative Templates -> VMware View Agent Configuration -> VMware HTML5 Features -> VMware WebRTC Redirection Features -> Enable Media Optimization for Microsoft TeamsAnd that’s it, you’re GPOs are now configured.
If you’re running a persistent desktop, run “gpupdate /force” in an elevated command prompt to grab the updated GPOs. If you’re running a non-persistent desktop pool, you’ll need to push the base image snapshot again so your instant clones will have the latest GPOs.
Confirming Microsoft Teams Optimization for VDI
There’s a simple and easy way to test if you’re currently running Microsoft Teams Optimized for VDI.
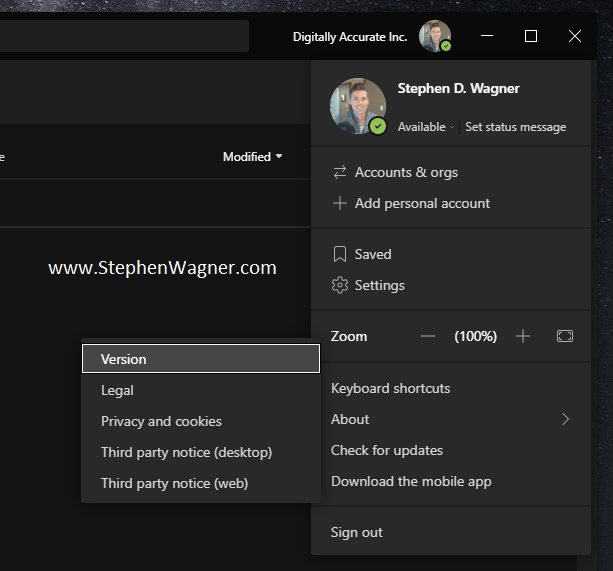
- Open Microsoft Teams
- Click on your Profile Picture to the right of your Company Name
- Expand “About”, and select “Version”
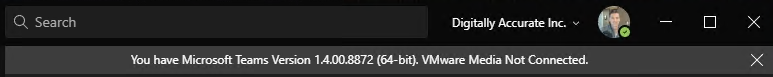
After selecting this, you’ll see a toolbar appear horizontally underneath the search, company name, and your profile picture with some information. Please see the below examples to determine if you’re running in 1 of 3 modes.
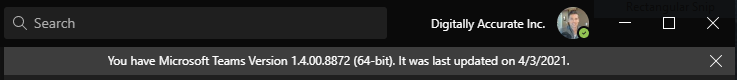
The following indicates that Microsoft Teams is running in normal mode (VDI Teams Optimization is Disabled). If you have configured VMware RTAV, then it will be using RTAV.
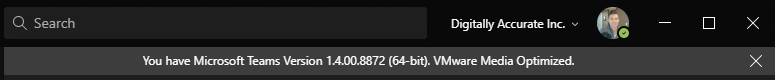
The following indicates that Microsoft Teams is running in VDI Optimized mode (VDI Teams Optimization is Enabled showing “VMware Media Optimized”).
The following indicates that Microsoft Teams is configured for VDI Optimization, however is not functioning and running in fallback mode. If you have VMware RTAV configured, it will be falling back to using RTAV. (VDI Teams Optimization is Enabled but not working showing “VMware Media Not Connected”, and is using RTAV if configured).
If you’re having issues or experiencing unexpected results, please go back and check your work. You may also want to review Microsoft’s and VMware’s documentation.
Conclusion
This guide should get you up and running quickly with Microsoft Teams Optimization for VDI. I’d recommend taking the time to read both VMware’s and Microsoft’s documentation to fully understand the technology, limitations, and other configurables that you can use and fine-tune your VDI deployment.